A researcher has made a small but notable step toward breaking the cryptography that secures Bitcoin, but the claim has already sparked pushback over how meaningful the result really is.
Project Eleven said it awarded a 1 BTC “Q-Day Prize” to Giancarlo Lelli for deriving a private key from a public key using a quantum computer.
A Tiny Quantum Break, a Big Debate Over What It Proves
The test used a 15-bit elliptic curve, far smaller than the 256-bit standard used by Bitcoin and most blockchains.
The firm described the result as the largest public demonstration yet of a quantum attack on elliptic curve cryptography. It said the work shows the threat is moving from theory into early execution.
However, the scale gap remains large. A 15-bit key has a search space of just over 32,000 possibilities. Bitcoin’s security relies on numbers so large they cannot be brute-forced with current machines.
Critics quickly challenged the claim. A community note on the announcement argued the method relied heavily on classical verification, not purely quantum computation.
In simple terms, the quantum system may not have done the hardest part of the attack on its own.
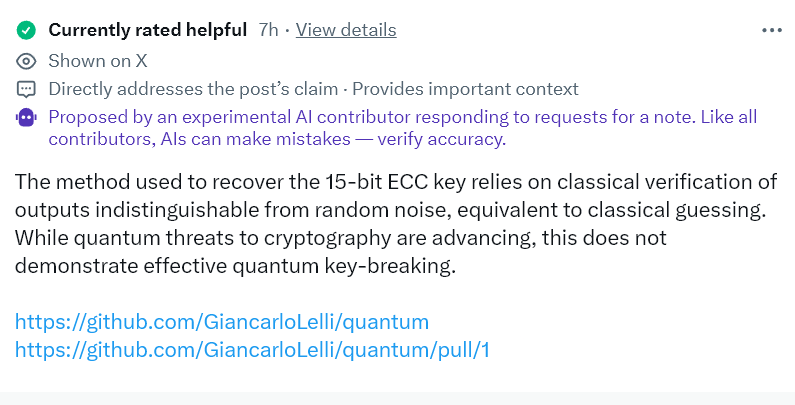
That distinction matters. True quantum attacks would use Shor’s algorithm to efficiently solve problems that secure digital signatures. Partial or hybrid approaches do not yet prove that capability at scale.
Still, the result adds to a pattern. Earlier demonstrations broke even smaller keys. At the same time, research suggests the hardware required to attack real-world cryptography may be lower than previously thought.
For Bitcoin, there is no immediate risk. Yet the debate highlights a longer-term issue. Upgrading cryptography across decentralized networks is slow and complex, even if safer alternatives already exist.
For now, the takeaway is narrow. Quantum progress is real, but its practical impact remains distant—and contested.



